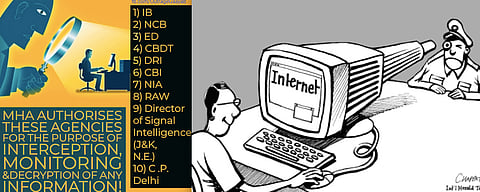
[dropcap]O[/dropcap]n December 20, 2018 the Central Government through the Ministry of Home Affairs brought out a notification in exercise of its powers under Section 69(2) and Section 87(2)(y) of the Information Technology Act, 2000 read with Rule 4 of the Information Technology (Procedure and Safeguards for Interception, Monitoring, and Decryption of Information) Rules 2009 — authorising a number of enforcement bodies, including the Central Bureau of Investigation, the National Investigation Agency, the Narcotics Control Bureau, the Research & Analysis Wing, the Intelligence Bureau, the Enforcement Directorate, the Central Board of Direct Taxes, the Department of Revenue Intelligence, the Director of Signal Intelligence and the Commissioner of Delhi Police, to act as "agencies" for the purposes of carrying out monitoring, interception and decryption of "any information" generated, transmitted, received or stored in any computer resource under the said Act.
Pertinently, the notification has generated wide-scale criticism amongst concerned citizens, civil society, media, social and cyber activists and even the State Government of West Bengal, which has issued a statement raising certain objections in the implementation of this notification. The Central Government has also given its reasons for issuing the notification and by relying on already existing statutory regime to accord validity to this notification.
As innocuous as the notification may seem, it does carry with it apocalyptic repercussions which may seriously affect the very federal structure of this country, imperil privacy of citizenry, bestow unfettered executive discretion at the hands of the agencies, all of which are in addition to the very notification being in direct conflict with the rules under which it has been passed, all of these factors having a cumulative, deleterious impact on the Rule of Law.
Section 69(1) confers power on the Central Government, the State Government or any officers authorized on their behalf to lay down directions pertaining to monitoring, interception and decryption of "any information" provided that such an order could only have been passed if the same meets with legitimate state interest. Legitimate State Interest under Section 69(1) of the Information Technology Act, 2000 pertains to protection of sovereignty and integrity of India, defence, security and friendly relations with nations, or for maintenance of public order, or for investigation of any offence or prevention of commission of any cognisable offence.
Subject to these riders, the safeguards and the procedure has to be laid down separately. It is in this background that the Central Government on October 27, 2009 made the Information Technology (Procedure and Safeguards for Interception, Monitoring, and Decryption of Information) Rules 2009 which laid down a detailed procedure to carry out such interception, monitoring or decryption of information.
Rule 4 of the 2009 Rules, says:
The competent authority may authorise an agency of the Government to intercept, monitor or decrypt information generated, transmitted, received or stored in any computer resource for the purpose specified in sub-section (1) of section 69 of the Act.
Rule 4, which seems to be the basis of the notification dated December 20, 2018 operates in a limited zone since it uses the expression "an agency". Rule 4 comes into operation on a case to case basis and does not require "multiple agencies" to be notified by way of a standalone omnibus notification like the present one. For instance, information reveals that a huge narcotics consignment is to be apprehended for which interception of an individual's computer resource may be necessitated. In such a scenario, on the basis of a prior actionable information, the Competent Authority may authorise the NCRB to carry out interception or monitoring. Rule 4 cannot be used as an umbrella provision to authorise every agency under the sun, for all times to come.
The choice of agency depends on the nature of case, the sensitivity involved and the network which is proposed to be intercepted or monitored and all these decisions have to be taken solely by the Competent Authority. By one notification, all agencies cannot be authorised to carry out interception or monitoring of "any information" on "any computer resource" for any case that may arise in future. The notification effectively denudes the power of the Competent Authority. The notification is, therefore, in complete and absolute abrogation of the Rules of 2009 itself. The notification also has the effect of curtailing the authority and the powers conferred on the Competent Authority since it is the order passed by the Competent Authority under Section 89(1) read with Rules 4 and Rule 10 which shall give the name of the agency, the name of the person or group of persons or their network which will be a subject matter of surveillance or interception and the particular officers entrusted with the task. Rule 4 nowhere contemplates issuance of an overarching notification which will have the effect of contravening Rules 9 and 10 since it is the statutory responsibility of the Competent Authority to appoint the agency on the basis of each case.
Rule 3 clearly states that no information could be made a subject matter of surveillance, monitoring, interception or decryption without the prior permission of Competent Authority. The Definition clause in Rule 2(d) defines Competent Authority to include only two designates, viz. the Secretary of the Ministry of Home Affairs and the Secretary in Charge of the Home Department of the concerned State or Union Territory. Thus it becomes clear that the principles of federalism have been kept in mind by the legislature, since the highest bureaucratic functionaries of the Centre and the State have been charged with the onerous task of passing orders to carry out surveillance. This is also in tune with the directions issued by the Supreme Court of India in the People's Union for Civil Liberties phone tapping case.
Rule 4 confers the Competent Authority to authorise an agency of the Government to intercept, decrypt or monitor information. The use of expression "an agency" leaves no manner of doubt that the mandatory precondition is the existence of such prior actionable information which the Competent Authority believes to be sufficient to authorise an agency to intercept or monitor. In terms of Section 69(1) the reasons of ordering such interception, monitoring, or decryption has to be in writing by the Competent Authority and it is then and only then that an order shall be passed by the Competent Authority to the agency in question calling upon it to carry out time-bound interception, monitoring or decryption not exceeding 60 days subject to a renewal only up to 180 days in terms of Rule 11 of the 2009 Rules. The contents of the directions contained in this order shall also have to be in writing as is clear from Rule 7 of the 2009 Rules.
Following steps emerge from the scheme of the Rules:
The overarching control still vests in the Competent Authority which is the Union Secretary, MHA or its State counterparts. The investigating agency concerned has to periodically submit its report to the Competent Authority apprising them of the status of such monitoring or interception on the basis of which further decision is taken by the Competent Authority whether to extend such an order or to revoke it.
Instead of requiring a prior permission from the Competent Authority, Rule 4 is being interpreted to mean that somehow the Competent Authority is delegating its essential functions to be carried out by the investigating agency which is untenable and preposterous. The scheme of the Rules of 2009 is that the decision to authorise an agency to conduct interception and monitoring vests solely in the Competent Authority, which then authorises an agency to carry out the actual interception in writing, specifically listing the nature of such directions, the duration and the targeted person(s), the name and designation of the officer from the concerned agency to whom such intercepted information shall be disclosed.
The MHA notification does away with the requirement of authorisation on a case-to-case basis and instead authorises every investigating agency thereby severely constricting the role of the Competent Authority. The agency concerned cannot assume to itself all the above mentioned roles, first to pass an order to its own officers to carry out interception and to also ascertain the feasibility of such interception. If all the agencies are already authorised to intercept or monitor any information, then this will render the very purpose of a Competent Authority nugatory. For the Competent Authority will not be able to carry out any of the roles and responsibilities envisioned under the scheme of the Rules 2009 and the requirement of his order in writing under Section 69(1) of the Information Technology Act, 2000 will be reduced to an empty formality.
From the scheme of the 2009 rules, it becomes manifestly clear that the power to authorise interception or monitoring has to be exercised from a case-to-case basis [Rule 9 of the Information Technology (Procedure and Safeguards for Interception, Monitoring, and Decryption of Information) Rules 2009] and every direction must contain the targeted individual or group of persons and no omnibus directions could be passed which the language of the notification seems to suggest, for it may have the effect of transforming a protective legislative instrument into a surveillance machine.
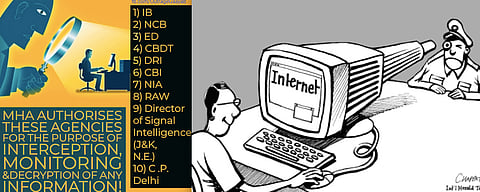
The MHA notification dated December 20, 2018 seems to convey the meaning that "any information" means "every information" available on every computer resource which will now be a subject matter of monitoring, interception or decryption by the agencies captioned in the notification for which purpose, various agencies have been "authorised". This interpretation, if allowed to stand, would throw open unchannelised, unrestricted and unfettered control for each of these agencies to carry out surveillance in real time, which is contrary to the plain and literal meaning of all the safeguarding provisions contained in Rules 3, 7, 8 and 9 of the IT Safeguard Rules, 2009.
If such an interpretation is accorded to the notification dated December 20, 2018 it would mean that each one of these agencies shall have the right to carry out interception, or monitoring of "any information" on any computer resource against all and sundry. This may include WhatsApp conversations, tweets and direct messages, Facebook wall posts, comments and Messenger texts, Snapchats, Instagram feeds or stories, blogs, vines, videos or information stored, retained or shared on email, cloud or any other digital platforms.
One can only imagine the nature and extent to which the Right of Privacy of citizens is threatened if the notification is allowed to stand. The multifaceted guarantees associated with the Right to Privacy which were recognised, protected and endorsed in Justice K S Puttaswamy case are under severe peril within months from the date of the historic decision.
Since preservation of law and order and criminal procedure are subjects which exclusively fall within the ambit of State List, it was an important consideration before the legislature which deemed it fit to confer that power on the Secretaries of the Union Home Ministry and his/her counterpart in the State to act as the Competent Authority. Where the scope of investigation or the criminality extends beyond the territorial limitation of a State, appropriate mechanism has been devised under Rule 6 which requires the Secretary in Charge of the Home Department of the concerned State to make a request to the Secretary of Home Affairs, Central Government, who in turn will make an order to this effect in writing.
The notification dated December 20, 2018 in a single stroke has demolished this crucial requirement, by authorising a number of enforcement bodies including the CBI, NIA, Narcotics Control Bureau, RAW, Intelligence Bureau, Director of Signal Intelligence and the Commissioner of Delhi Police to act as "agencies" irrespective of the nature of the case even in those areas which are beyond their jurisdiction.
To illustrate, for a case which requires an interception to be conducted in Chhattisgarh and Madhya Pradesh, the Commissioner of Delhi Police cannot assume the role of an interception agency by any stretch of imagination. Most of these agencies require a prior authorisation to investigate by the State Government or the Central Government to take up investigation when the matter is beyond their local jurisdiction. This notification, however, does away with that requirement by effectively "pre-authorising" each of these agencies to carry out monitoring, interception and decryption at their will.
As is now evident, the word "authorise" in Rule 4 presupposes that there already is a tangible actionable information which necessitates the order of directing interception. If there is no alleged wrongdoing which may give credible reasons to the Competent Authority to order interception or monitoring, then the question of authorising any agency does not even arise. Yet, a notification such as the present one comes out and authorises multiple agencies without any alleged suspicious case existing, which leads to one of the two consequences. Either the State suspects that every citizen is under suspicion of having conspired or committing an offence or is otherwise a potential criminal. Or the State believes that the requirement of authorising a particular agency is only an empty formality and any agency which is pre-authorised can assume to itself the role of carrying out surveillance, interception in a particular case, irrespective of whether the same agency is also an investigating agency. Both these situations are equally catastrophic in their own might.
Since Rule 4 nowhere contemplates the issuance of an omnibus notification, the very issuance of the notification is de hors the provisions of law, it does not further any Legitimate State Interest; on the contrary, it is against the very Rules under which the notification has been passed, leading credence to the widely-speculated belief that the notification may be one of the many steps to create a cyber surveillance infrastructure. The notification in its sum and substance confers wide and excessive delegation of powers to the agencies, which is not even contemplated within the Rules. The notification runs contrary to the Rules formulating it, and also denudes the powers of the Competent Authority and reduces it to a mere signing authority. The notification has a tangible perilous effect on the constitutionally guaranteed rights of the citizens, particularly informational privacy which has been recognised as an essential facet of an individual's liberty. One can only hope that the PUCL and Shreya Singhal sagas are not repeated again.
The author is an advocate practising in the Supreme Court of India.
[Banner image courtesy: International Herald Tribune; Outrage Gaayab.]